I've been programming for personal purposes since 1986. At that time I autodidactically began learning BASIC with the help of two books. I wrote the first "programs" on paper because I didn't own a computer back then. Only 1989 I bought my first computer - a ZX Spectrum. I developed in Z80 assembler for the first time. Until then I only had the opportunity in informatics lessons at school to use a KC-85/3. From 1988 I began using Turbo Pascal as well. The needed computers were provided during my study: KC-85/3, KC-87 and PC 1715. I bought my first "real" PC in 1991: a 386 SX/20 with 4 MB RAM. I wrote many small applications around the operating system (MS-DOS 6.2) and the graphics card in Turbo Pascal and Assembler with it. I began programming Windows (WfW 3.11) in 1995 - this time in Visual Basic 3.0 and Turbo Pascal for Windows. After 1998 under Windows 98. Especially with Delphi and Visual Basic 6.0. Beginning 2006 with Visual Basic 2005 (.NET Framework 2.0) and Turbo Delphi as well.
Subsequently I provide a small collection of applications as freeware for common usage. I can provide the source code as well, if needed. All programs are without an installer. Just download and unpack them into an empty directory (I recommend WinRAR or 7-Zip, if you don't want to pay anything). I cannot be held responsible for any damage while using the applications. The files are free of viruses or trojans and I use them all for personal needs.
There seems to be a big interest in my NTFS tools. That's why I placed the Delphi sources here. Have fun.
Alexander Freudenberg
 |
DuamonXP
In early versions of GetRight there was a little traffic display in the lower right corner. I converted this display into a separate application. The small windows can be moved freely on the desktop and is always shown in foreground. This version of the program only supports dial-up adapters (modem, ISDN). |
|
 |
Ethermon
This application monitors every network traffic and shows it in the same manner as DuamonXP. Ethermon uses the funktion GetIfTable from iphlpapi.dll. |
|
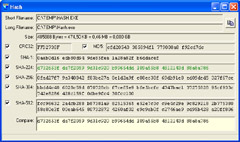 |
Hash
Using Hash you can show and compare the hash values MD5, CRC32 and SHA-1, SHA-224, SHA-256, SHA-384 and SHA-256 for any file. |
 |
 |
JumpReg
JumpReg can be used to "jump to" a given registry entry, for instance copied from a web site, in Regedit. Similarily as it does Registry Monitor from www.sysinternals.com. |
|
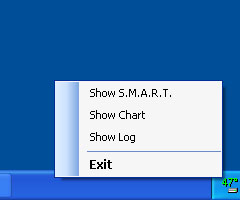 |
hdTempLogger
My first .NET-2.0 program. It uses WMI functions to show the temperature for the first connected hard drive in the tray area and a chart. S.M.A.R.T. values can be displayed alongside.
|
|
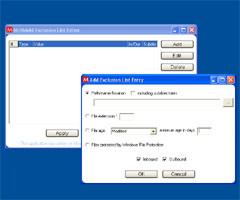 |
MELE
Abbreviation for McAfee Exclusion List Editor. There is a built-in option in VirusScan 9.0 and 10.0 to exclude several files and directories from being scanned by the on-access scanner. But there is no GUI from McAfee. My program closes this gap.
|
|
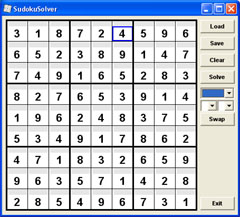 |
SudokuSolver
The Sudoku wave gripped germany in 2005 too. Instead of solving the many puzzles with the troublesome pen algorithm I had more fun in writing a programmatical solution aid. Thus the Sudoku phenomenon was history for me.
|
|
 |
WinEnumPS
Reading the book "Windows Internals" by Mark Russinovich and David Solomon inspired me, to explore the virtual address space of user processes using the VirtualQueryEx function. WinEnumPS lists all processes and the DLLs and memory mapped files mapped into their address space. You can display the maximum available virtual memory for a process (for instance DLLs that have their preferred base address at 10000000h, are responsible for the fact that only 1200 MB contiguous memory can be allocated by VirtualAlloc in Delphi). The memory allocation can be shown as a graphic. Additionally every memory range of all processes can be viewed in detail. The SeDebugPrivilege is requested to accomplish that.
|
|
 |
TXTEVTVWR
With TXT Event Log Viewer you can view event log files in TXT or CSV format. The file formats of a direct export from eventvwr.exe or created by MPSReports tools are supported (dumpel.exe). Needs .NET Framework 2.0.
|
|
 |
WhoIsIt
WhoIsIt serves the purpose to learn names of persons. In the program directory of whoisit.exe there has to be a file named list.txt with the names and picture files in the following structure: "name;file_name_including_path". A status file is saved in the AppData directory of the user.
|
|
 |
ImageScan
Using this program a directory structure can be searched for executable files. Internal information and flags are listed for every found application and DLL.
|
|
 |
Internet
Explorer Cache Manager
Allows access to the content, cookies and history entries of the index.dat. The cache entries can be deleted indvidually or alltogeter. The functions FindFirstUrlCacheEntry and FindNextUrlCacheEntry as well as DeleteUrlCacheEntry from wininet.dll are used.
|
|
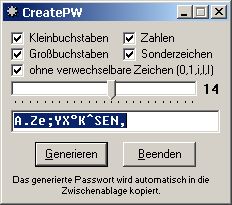 |
CreatePW
Creates a random password of configuarable length.
|
|
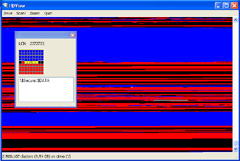 |
HDView
Works similarly like Diskview from www.sysinternals.com with the difference, that the exact position of system files (like $MFT or $Secure and so on) and their attributes on NTFS volumes is displayed as well. The application uses the DeviceIoControl functions FSCTL_GET_NTFS_VOLUME_DATA, FSCTL_GET_NTFS_FILE_RECORD and FSCTL_GET_VOLUME_BITMAP. I recommend the free defragmenter JKDefrag to clean up the mess.
|
|
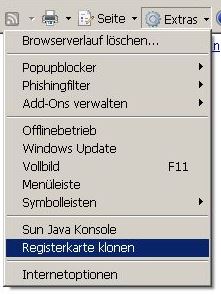 |
Clonetab
There is no option in Internet Explorer 7.0 to create a duplicate of the currently open tab. That's why I wrote a browser extension that implements an additional menu entry under "Tools" . To install the extension copy the file clonetab.exe from the archive into the directory "C:\program files\Internet Explorer\Exec". After that the extension as to be registered by executing the _install_en.reg. The following entries are made: [HKEY_CURRENT_USER\Software\Microsoft\Internet
Explorer\Extensions\{1D32B349-02E3-47c4-8A17-59FE88810590}]
|
|
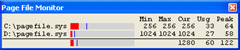 |
PagefileMon
Monitors the usage of paging files.
|
|
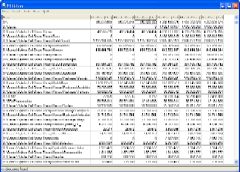 |
NTFSTree
Lists all file and directory objects of a NTFS volume and adds up the file sizes for the directory including all files and subdirectories. Thanks to the direct access to the MFT this operation is very fast. The file sizes listed in the MFT and the actually used clusters for the attributes and streams of a file are shown. The sizes of the hidden NTFS system files are displayed as well. Hint: If files are shown multiple times, this is no bug. NTFS sometimes creates several file entries with a part of the entire amount for one single file.
|
 |
 |
NTFSniffer
Creates an
index of a complete NTFS drive within a
few seconds and allows a full-text search for file names. The search
result are immediately shown while the search text is being entered.
Usage: NTFSniffer <drive letter:>
|
|
 |
NTFSDelta
Another program based upon my NTFS routines. It can be used to examine changes on the file system. It works on the snapshot principle. A snapshot takes just a few seconds.
|
|
 |
CleanOutlookCache
It happens occasionally that you are unable to open or save attachments in Outlook. The reason for that is, that the OLK folder, which Outlook is using to store temporary files, contains too many files. With this program you can empty the cache.
|
|
 |
NTFSTop
Shows the
largest files on the selected volume.
|
|
 |
SpecialFolders
Shows all available Windows special folders by means of SHGetSpecialFolderPath (VB 2008).
|
 |
| console application | SysEnum
Lists all loaded drivers and their position in kernel memory. Supplement to driverquery. Can be used to assign blue screen memory positions to a driver (if the drivers are loaded to the same position at every system start) |
|
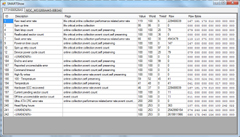 |
SMARTShow
Shows
the S.M.A.R.T attributes of all
attached hard disks. Requires .NET Framework 4.0.
|
|
 |
HDAligncheck
Checks if the partitions of the system are aligned to "round" offsets. This is especially important for SSD disks. Requires .NET Framework 4.0.
|
|
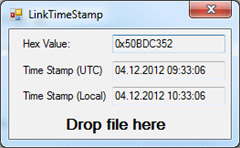 |
LinkTimeStamp
My first C# application. It can be used to convert a time_t value into a readable date format. The time stamp of an executable or dll is stored in this format and occasionally shown in connection with EventID 1000 in the event log. The Dependency Walker shows Link Time Stamp in a column. Including source. |
 |
 |
TurboBoostUI A couple of years ago Intel published a Sidebar Widget that could show the Turbo Boost status of Core i7 and Core i5 processors. Because Windows stopped supporting Widgets in later versions I recreated the functions in a standalone application. All Turbo Boost capable processors of all generations are supported. .NET Framework 4.5 is required. Developed with Visual Studio Community 2015. |
 |
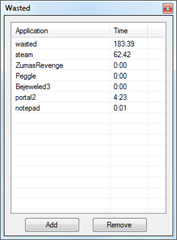 |
Wasted This program monitors the list of active processes and increases a counter for selected processes once a minute. Thus the runtime of games etc. can be measured. You may want to run this program on every boot by putting a new registry entry in HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run that points to the location of the wasted.exe |
 |
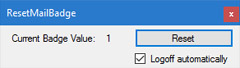 |
ResetMailBadge Issue: The Mail App for Windows 10 shows a wrong number of unread emails in the live tile and at the task bar icon (a number in a circle - the so-called "badge"). I have already marked all possible emails as unread and read again. Even a reboot doesn't solve it . What can I do? The badge is stored in a database %localappdata%\Microsoft\Windows\Notifications\wpndatabase.db. Apparently the value was not updated correctly at some time before. To solve it, one could edit the record manually as I describe it here. With this application the process is automated . Please create a manual backup of the SQLite database first. |
 |
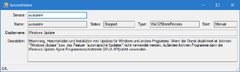 |
ServiceName Determines the display name for a known Windows service name. |
 |
| Toaster There is a notification area in Windows 10 on the lower right side of the screen. Here so-called toast messages can be shown by different applications. With my toaster.exe you can display your own messages there. Usage: toaster.exe "This can be your own message text." This is especially useful whe you want to be informed about event log messages right when they occur. You can assign a scheduled task with a certain event as a trigger ("Attach task to this event..."). You run toaster.exe and pass the required message as command line argument. Example: "Package $(PackageIdentifier) failed to be changed to the $(IntendedPackageState) state. Status: $(ErrorCode)" You need to export the task job as xml and put the following lines under the closing </Subscription> tag: <ValueQueries> <Value name="EventID">Event/System/EventID</Value> <Value name="ErrorCode">Event/UserData/CbsPackageChangeState/ErrorCode</Value> <Value name="PackageIdentifier">Event/UserData/CbsPackageChangeState/PackageIdentifier</Value> <Value name="IntendedPackageState">Event/UserData/CbsPackageChangeState/IntendedPackageState</Value> </ValueQueries> Delete and re-import the task. See http://aymanstechblog.blogspot.de/2012/05/passing-event-details-as-arguments.html |
 |
|
| ModalAlert Shows a notification message in the foreground. Usage: ModalAlert "And now for something completely different ..." |
 |
|
| nop Starts a process and ends it immediately. Usage case: If you want to prevent the execution of an application, you can define nop.exe as debugger. Instead of the application the nop.exe is executed and nothing happens. Example: In the registry the following REG_SZ entry must be created if you don't want Chrome to scan the system for software. [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\software_reporter_tool.exe] "Debugger" = "C:\Tools\nop.exe" |
 |
|
| DS2FullScreen There is an issue in the game Dungeon Siege II (Dungeon Siege 2, DS2) on Windows 10. The main screen opens, but the mouse cursor is not visible and thus the game cannot be started. The workaround is to start the game in windowed mode and switch to fullscreen later with tools like Fullscreenizer or Borderless Gaming. My DS2Fullscreen application only checks for the DungeonSiege2.exe and switches it to fullscreen. Usage: Add the following command line switches ("Set launch options") to the game in Steam: fullscreen=false width=1920 height=1080 nointro=true . Start the game as usual and confirm the error message that it cannot switch to the given resolution. Then run D2Fullscreen.exe with administrator permissions. Done. |
 |
|
 |
Akkumon Shows the battery status on the desktop. |
 |
last
change: 12/02/2024